Published Mar 11, 2022 by Xiph
Protecting your business from cyber attacks involves understanding all the types of malware that can derail your operations and how you can best prevent them.
There were over 67,500 cyber attack reports made to the Australian Cyber Security Centre in 2021, an increase of 13% year-on-year. Small businesses filed a higher number of cybercrime reports than in the previous financial year; while medium businesses had the highest average financial loss per cybercrime report. There were also nearly 500 ransomware cybercrime reports, an increase of nearly 15% from the previous period.
Cyber attacks are on the rise in Australia and the modern world more broadly − it’s now more important than ever to safeguard your business against malware and other cyber security threats that could derail your operations or organisation. The first step in protecting your business and digital assets is to know about the different types of malware and how to best prevent them.
What is malware?
Malware − short for malicious software − is an umbrella term that describes any type of intrusive software designed to infiltrate, exploit and disrupt programmable devices (including computers, smartphones, or tablets), networks, or operating systems. Cybercriminals typically use malware to target businesses, usually to exploit commercially confidential data or block access to information for financial gain. Individuals can also be targeted which may lead to identity theft or the theft of credit card information or other financial data. Trojans, viruses, and ransomware all fall within the category of malware, in addition to other threats. The best way to protect your business from malware infection is through prevention.
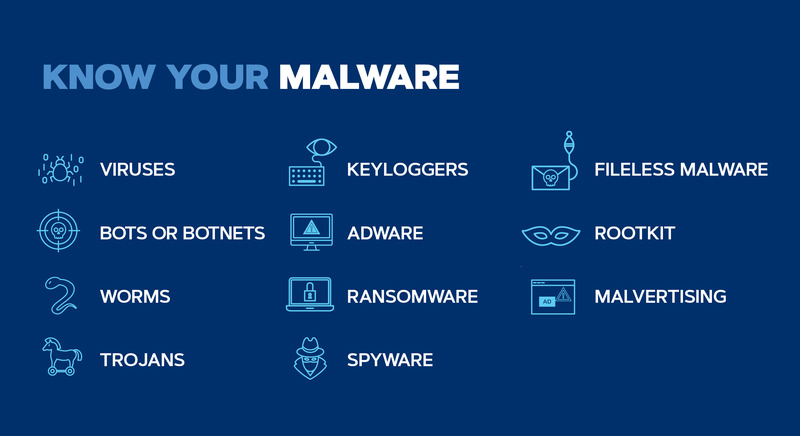
What are the different types of malware?
Malware can come under the guise of legitimate digital links, content, or assets. Here are the most common types of malware and how they work:
- Viruses
- Worms
- Trojans
- Ransomware
- Bots or botnets
- Adware
- Spyware
- Rootkits
- Fileless malware
- Keyloggers
- Malvertising
1. Viruses
A virus infects computer programs and devices and can also spread to other systems, in addition to performing its own malicious work. A virus usually comes as an attachment or file sent by an end-user to infect a device or software program. A virus only spreads when the file/attachment is opened by the person or business targeted. This type of malware can encrypt, corrupt, delete or move data and files.
2. Worms
A worm can infect devices or systems on the same network and spread (just like a virus) to other devices without end-user action. This type of malware exploits security vulnerabilities in devices or operating systems to infect networks, but doesn’t infect other programs. Worms are typically inserted via a malicious link or file.
3. Trojans
A Trojan is disguised (like a Trojan horse) as a legitimate code or software that contains malicious coding or instructions. Victims are often ‘tricked’ into downloading or using Trojans. Once up and running, this type of malware can access sensitive data, crash a device and launch subsequent cyber attacks. Trojans can be hidden in anti-virus programs, games pop-up ads, and even be embedded in attachments in phishing emails.
4. Ransomware
Ransomware is a type of malware that encrypts files or data, therefore, rendering that information unusable, until a ransom is paid. Hackers typically block access to important files or information or threaten to publish that information unless the victim or business pays the ransom. Ransomware attacks are common in business and usually place an organisation in a position where paying the ransom is the easiest (not the cheapest) way to regain access to vital files or data.
5. Bots or botnets
A bot is a malicious software application designed to hijack and spread to various computer devices and create a network of bots (also called a botnet) that performs automated tasks on command without end-user interaction. This type of self-propagating malware can also connect back to central servers created by the malware bot instigators. However, not all bots are malware, some internet bots like spiders, crawlers, and web bots are used for web crawling and indexing pages on search engines like Google.
6. Adware
Adware is unwanted or malicious advertising. This type of malware typically comes in the form of pop-up ads and uses ‘spammy’ advertising to collect an individual’s data and information without their consent in order to serve them more personalised ads. Adware can also impact businesses, if an employee inadvertently clicked on adware or a look-alike web page with adware, for example. Adware can compromise a business’ commercially sensitive data and even lead to users downloading more harmful types of malware unintentionally.
7. Spyware
Hackers typically use spyware (a type of malicious software) to monitor online activity and steal or gather information about a person or organisation which then gets relayed to a third party for exploitation or financial gain. This may include key logs, passwords to various accounts, pins, credit card, and financial information, web browsing data, and more. Spyware can also be used on desktop and mobile browsers.
8. Rootkits
A rootkit is a type of clandestine software that enables unauthorised users (hackers) to remotely access and possibly control a computer undetected. Rootkits can also conceal other malware, like keyloggers or spyware. This type of malware can affect a computer’s performance and steal personal or commercial data and can sometimes also conceal other malware, like keyloggers and viruses. Rootkits can be spread through phishing emails, malicious attachments, or compromised shared drives.
9. Fileless malware
As the name suggests, fileless malware doesn’t rely on executable files to infect a computer or device. Instead, it uses native or legitimate programs like Microsoft Office, PowerPoint, and other system tools to infect a device. It’s difficult for anti-virus software to target and prevent fileless malware because this type of malware is largely undetectable and leaves no files behind. Fileless malware can exploit even the most sophisticated security systems.
10. Keyloggers
Keylogger is a type of spyware that records keystrokes and online activity. Hackers can then use this information to access financial data and other sensitive information and get unauthorised access to accounts. Keyloggers are typically inserted via phishing emails, malicious downloads, or social engineering. However, not all keyloggers are malware – some businesses use them to monitor employee activity online and data usage.
11. Malvertising
Malicious advertising or malvertising for short (not to be confused with adware) uses legitimate website ads with an embedded malicious code to deliver malware to a computer. Once clicked on, the ad with the malicious code will redirect users to malicious websites or install malware on a computer itself. In some cases, an ad may execute automatically without being clicked on, a process referred to as a ‘drive-by download.’
Malware vs virus: Is there a difference?
Malware and viruses are often used interchangeably, but they’re not quite the same nor too different either. Malware is the catch-all term that describes all types of malicious software, while a virus is just a specific type of malware (among many) that uses a malicious piece of computer code to self-replicate and infect different programs and systems (like a human virus). In short, all viruses are malware, but not all malware is a virus.
How is malware injected or installed?
Most malware is injected without the consent of the user or business, typically through a malicious code or application attached to a file or link. Hackers don’t always use sophisticated technology or techniques to launch cyber attacks. Common methods to launch malware include phishing emails, fraudulent websites, hard drives, compromised software, dodgy downloads, fake ads, and applications.
How does malware affect your business?
Malware is the biggest security threat for small-to-medium businesses and big corporations alike and can devastate an organisation in more ways than one. This includes disrupting or disabling systems and networks to disrupt or shut down business operations, or by breaching data security or leaking sensitive information which could lead to identity theft and financial extortion. In some cases, malware can also damage an enterprise’s reputation and operations in the market.
Common signs of malware
The first step to beating malware is to identify it quickly before it spreads to other systems or networks. Here are some common tell-tale signs of malware infection.
- Changes in security settings or disabled security tools
- Reduced computer and system performance
- Problems shutting down or starting up computers
- Finding new programs or desktop icons not recognised
- Inexplicable computer freezes or crashes
- Frequent or suspicious pop-up ads
- Security warnings (sometimes with solicitation to buy something to fix security issues)
- Unintended browser redirects
- Ransom demands
How to protect your business against malware
Prevention is always the best protection against malware. This is best done by keeping your operating systems and applications updated and encrypting sensitive data to prevent it from falling into the wrong hands. In addition, modern businesses should take a multi-pronged approach to cyber security and invest in a multitude of security tools that will work together to provide the best defence against sophisticated cyber attacks. Security tools businesses should invest in include:
A firewall: a piece of software or hardware that monitors all incoming and outgoing traffic to your computer. A firewall creates a barrier between your internal network and traffic coming from external sources (such as the internet) to block malicious software from infecting your computer or unsolicited traffic. Setting up a firewall adds a layer of protection to your business’s internal networks.
Security software: security tools like anti-virus software, anti-spyware software and anti-spam filters can provide comprehensive anti-virus scanning as well as detect and block malware infection. Anti-virus software should be installed on all devices and set to automatically check for updates and alerts. Only purchase security software from a reputable company.
Spam filters: a piece of software that detects or blocks spam and phishing emails received. A spam filter typically sits behind the firewall of a network to identify email threats coming from external sources.
Cloud data protection: encrypting and backing up sensitive data in a cloud environment can prevent it from falling into the wrong hands and ensure the continuation of the business, even in the event of a malware attack. Encryption converts data into a secret code to reduce the risk of theft or tampering.
A final word
Each business is unique and will require different levels of protection against malware. We provide advice to businesses and offer tailored cyber security solutions for all types of businesses and industries. Contact us via email for more information: enquiries@xiphcyber.com.
Posted in: Security