Published May 18, 2023 by Xiph
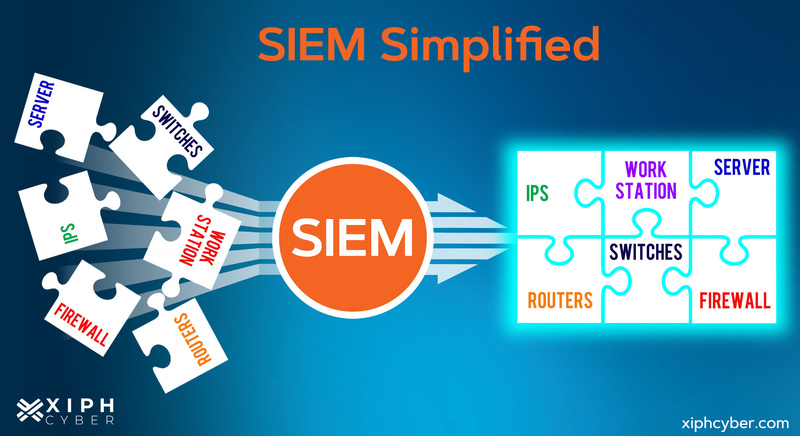
Businesses spend a lot of time and money staying ahead of threat actors and preventing cyber breaches. Security information and event management (SIEM) can help automate your organisation’s threat detection and incident response.

What is SIEM?
SIEM, pronounced “sim”, is an important component of cyber security that helps organisations detect, analyse, and respond to security threats before they have a chance to disrupt business assets and operations. SIEM combines both security information management (SIM) and security event management (SEM) tools into one security management system.
At their most basic level, all SIEM solutions collect and consolidate data from a range of sources to detect cyber threats and adhere to data compliance requirements and identity activity that deviates from the norm. Most modern SIEM solutions use artificial intelligence (AI) and algorithms to provide more real-time threat analysis. The technology learns with each incident and gets better at thwarting modern threats. SIEM software solutions can be stored on-premises or in the cloud.
SIEM features & benefits
SIEMs are a staple of security operation centres (SOCs) and offer many benefits that can improve your business’ overall security posture, including:
- User and entity behaviour analytics (UEBA): Real-time monitoring of users, applications, and devices. This detects both normal and abnormal behaviour in a corporate network and at endpoints.
- Advanced malware/threat detection from endpoint to perimeter: Collects logs (records of events from anywhere within a network and on the perimeter.
- Consolidation of security capabilities into one system: SIEM provides log management, event correlation, and incident monitoring and response, in one place.
- Log management and retention: SIEM collects logs and correlates them with other security information into a central repository for analysis and archiving.
- Incident response and continuous monitoring: Can detect patterns and trigger alerts for any anomalies and automate incident response processes.
- Analytical dashboard for data aggregation & forensic analysis: Pre-configured or customisable dashboards present a larger picture of aggregated log data from different sources and actionable insights.
- Notifications & alerts: Set up alerts and notifications for any irregularities in a network and positive matches (logs match that rule for a real threat).
- Streamline compliance auditing and reporting: SIEM reporting tools can generate various reports and correlate logs to meet regulatory compliance and auditing requirements.
- Low cost: Basic SIEM solutions are affordable in most scenarios.
How does SIEM work?
SIEM comprises many monitoring and analytics components, supporting the incident response capabilities of your SOCs. SIEM technology collects and analyses data from different sources within a network infrastructure from perimeter to end user in real-time. Data sources can include:
- Web applications
- Servers
- Network devices (i.e. routers, modems, etc.)
- Security devices (i.e. firewalls, VPN gateways, etc.)
- Cloud & SaaS solutions
- Hybrid environments
- On-premises assets
- External users.
SIEM then examines data from these sources to find usage patterns and detect abnormal ones. Some patterns are considered threats to be closely monitored, and alerts will be issued to further investigate.
For example, a user logging into their account once in 10 minutes may be considered normal, but a user trying to log in 100 times in just a few seconds might indicate a brute force attack. This is how SIEM detects and flags potential security threats and attacks. Cyber attacks will be dealt with in real time before they can impact operations.
How to implement SIEM in your business
The first step in implementing SIEM technology effectively is to define its scope. Take stock of your current security stack and threat landscape. Design policy-based rules that define activities and logs your SIEM software should monitor. Consider your business compliance requirements to ensure your SIEM solution is configured to audit and report on these standards in real-time so you can better understand your risk posture.
Then, you can set up your SIEM system to monitor your most critical IT assets and resources like databases, firewalls, routers, wireless access points, and cloud assets. Connect your SIEM tool to as many data sources so it can bring all data to a central location or dashboard to monitor it. You can use pre-configured data correlation rules or get your security team to configure new rules based on your organisation’s specific needs and requirements. Different policies related to IT configuration and Bring Your Own Device (BYOD) may be established to monitor remote login attempts and privileged and administrative access.
Don’t set and forget. Continue to fine-tune your SIEM configurations to reduce false positives and alert fatigue in your security alerts. Lastly, be sure to have an incident response plan in place so that your business can quickly respond and mitigate any type of cyber attack and prioritise the recovery of the most critical assets.
A final word
SIEM is an important part of an organisation’s cyber security ecosystem. It gives IT and security teams a central system to manage huge volumes of data and logs across your business, and operational capabilities to help manage compliance requirements. For more information, contact us via email: enquiries@xiphcyber.com.
Posted in: Security