Published Jun 17, 2022 by Xiph
Everyone uses encryption technology on a daily basis, whether that’s when surfing the interning, storing data in the cloud, or working for a business that processes tons of private data. While most of us probably don't understand the ‘how’ or ‘why’ − encryption is vital to keeping sensitive information private and out of the hands of unscrupulous actors. This guide explains what encryption is and how it works.
What is encryption?
Encryption is a way to scramble data and information (think of it as turning it into a secret code) so that it can only be read by authorised parties – those with the decryption key. It helps to protect the confidentiality of digital data either stored on computer systems or sent through a network or the internet.
How does encryption work?
At its most basic level, encryption converts human-readable plaintext into unreadable text, known as ciphertext. Formulas called encryption algorithms, or ciphers encode readable data and make it look appear random to all but the intended owners or recipients of that data. Encryption also uses a cryptographic key: a set of unique mathematical values that both the sender and the recipient of an encrypted message/data agree on. Secure/effective encryption uses keys complex enough that a third party is highly unlikely to decrypt or break the ciphertext by guessing the key (or by brute force attack).
Encrypted data gets decoded and translated back to its original form whenever any of the intended users or recipients access it – this is called decryption. To unlock the message, both the sender and the recipient need the ‘secret’ decryption key to unscramble the data back to a readable plaintext. Data can be encrypted ‘at rest’ when stored (i.e. on a USB, hard drive, smartphone, etc.), or while ‘in transit’ when transmitted around networks (i.e. on the internet, emails, between servers, etc.).
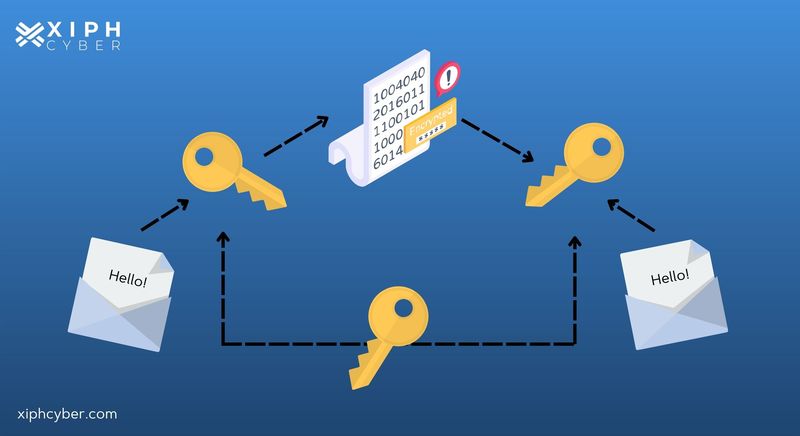
What is a cryptographic key?
A cryptographic key is a string of numbers or letters within an encryption algorithm that can encode or decode cryptographic data. Like a physical key, it locks (encrypts) data so that only users with the right key can unlock (decrypt) it.
Why is data encryption necessary?
Encryption safeguards and protects your sensitive data and business information from internal and external threats – it ensures that even if an intruder gained access to your business information, they’d be unable to read any of it. Data encryption is a basic, but vital security measure for both small and medium-sized enterprises (SMEs) and big businesses with a great deal of private information. Businesses commonly use encryption to secure data like emails to protect sensitive information sent through email channels, data stored in the cloud or hard drives, client files, or electronic payment information (which is subject to strict security standards).
How does encryption keep internet browsing secure?
Encryption is also vital for protecting data and communications between a browser and website server using a secure protocol like HTTPS (Hypertext Transfer Protocol Secure). HTTPS uses encryption protocols like Secure Sockets Layer (SSL) or Transport Layer Security (TLS) to provide encryption in transit to ensure that even if data packets were intercepted, they couldn’t be read or tampered with.
What are the different types of encryption?
There are two main types of encryption − symmetric encryption and asymmetric encryption.
- Symmetric encryption: uses only one cryptographic key that all communicating parties use to both encrypt and decrypt data.
- Asymmetric encryption: (also known as public key encryption) uses two keys − one for encryption and a different key for decryption. A public key shared among users is used to encrypt the data, while a private key, which is not shared, decrypts the data. Asymmetric encryption is a foundational technology for TLS and SSL.
What is an encryption algorithm?
An encryption algorithm or cipher is a set of rules used to convert readable data into ciphertext. Data scrambled by encryption algorithms looks like randomised code made up of letters, numbers, and symbols. But of course, encryption algorithms configure ciphertext or scrambled data in a purposeful way, so that it can easily be turned back into plaintext by a decryption key.
What are the most common encryption algorithms?
Here are the most common and widely used encryption algorithms:
Advanced Encryption Standard
Advanced Encryption Standard is one of the best encryption protocols to protect the transfer of data online. In fact, it’s the standard method of encryption of most government agencies and is used worldwide. It’s a symmetric block cipher that encrypts data on a per-block basis. The size of each block is usually measured in bits and AES operates on a fixed block size of 128-bits (or 16 bytes). However, it gives three possible lengths of AES encryption keys. Each key length has a different number of possible key combinations: 128-bit keys, 192-bit keys, and 256-bit keys. The longer the key, the stronger the encryption.
Triple DES
Triple DES (3DES) is also a symmetric block cipher that applies the Data Encryption Standard (DES) cipher algorithm to encrypt blocks of data three times using a 56-bit key. It encrypts, decrypts, and encrypts data again – hence the ‘triple’. The plaintext is encrypted with key 1, then that text is encrypted using another key (key 2) and finally, key 3 encrypts the last message or text. Triple DES is an advanced form of the DES method. 3DES is widely used by financial institutions to encrypt ATM PINs and credit card transactions.
TwoFish
TwoFish is considered one of the fastest encryption algorithms and is free for anyone to use. It’s used in both hardware and software to encrypt data blocks of 128 bits. Twofish always encrypts data in 16 rounds regardless of the key size. Twofish encryption works slower than AES but is still used by some file and folder encryption software solutions.
RSA
Named from the familial initials of three computer scientists − Rivest-Shamir-Adleman (RSA) − is an asymmetric encryption algorithm that creates and publishes a public key based on two large prime numbers, along with an auxiliary value. Messages can be encrypted by anyone, via the public key, but can only be decoded by someone who knows the prime numbers. RSA is a relatively slow algorithm and is no longer commonly used to directly encrypt user data.
A final word
Encryption is a basic but vital component of data privacy and security. A great deal of private information is transmitted online 24/7, so it’s important to keep it safe from unauthorised users. If you’re wondering which encryption solution is best for your data and business, contact us via email: enquiries@xiphcyber.com.
Posted in: Security